For the past two years, our advocacy efforts have been strictly focused on regulations proposed in California and at the Federal level. This was a strategic decision, given our small and burgeoning status in the policy landscape.
ISL has been following the California Privacy Protection Agency’s journey from its inception and has been participating throughout the preliminary and formal rulemaking process. Since 2021, we have provided two sets of written comments here and here. Continuing in that tradition, ISL recently submitted a public comment on the proposed California Consumer Privacy Act Regulations, released on July 8, 2022. We voiced our support for many of the principles introduced in the proposed regulations and submitted our ISL Consumer Safety Scorecard to the California Privacy Protection Agency addressing a few of our safety concerns with the proposed regulation.
ISL Consumer Safety Score for CPPA Regulations
The overall ISL Consumer Safety Score for just the proposed regulations was:
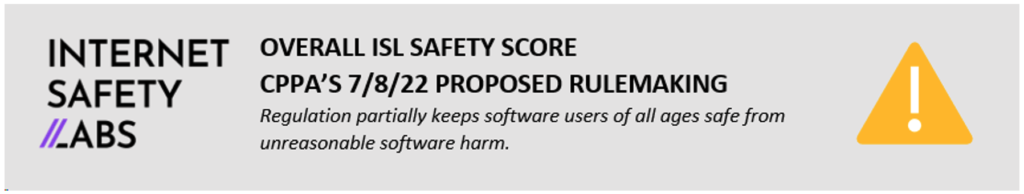
A couple things to note regarding our scorecard, it is difficult to achieve a high score due to the volume of programmatic harms inherent in software these days. Here are the key factors that went into the score:
- Regulation does not provide complete and accurate notice including the identification of all third-party entities.
- Regulation does not require B-s that process large amounts of personal information to owe a duty of loyalty.
Introduction to the Scorecard
The ISL Consumer Scorecard compares the text of the proposed California Consumer Privacy Act Regulations, released on July 8, 2022, against ISL regulation safety criteria listed below. Note that this scoring does not reflect the overall CPRA regulations.
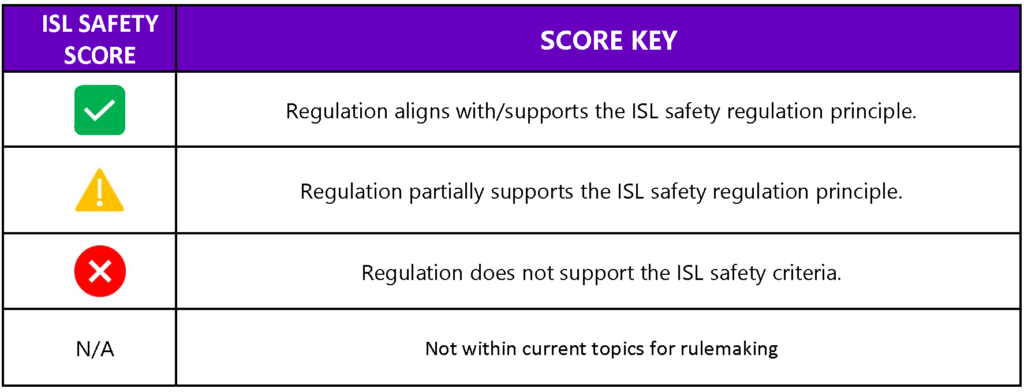
Legend
Terminology Mapping
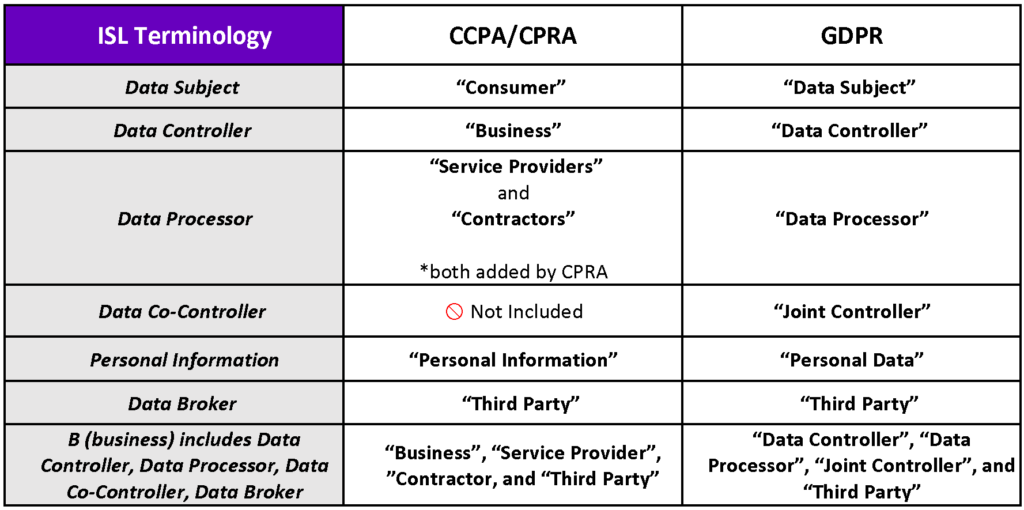
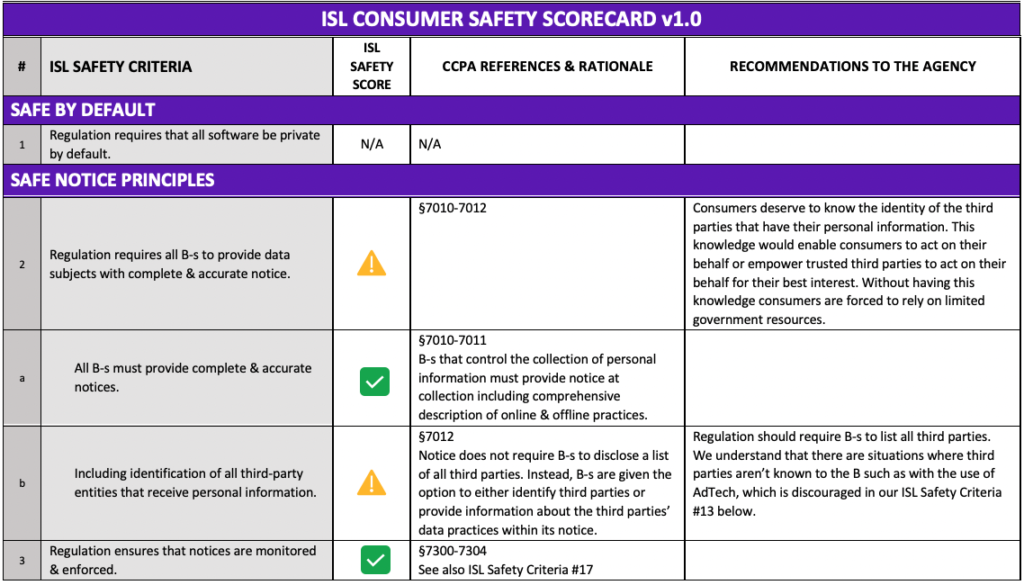
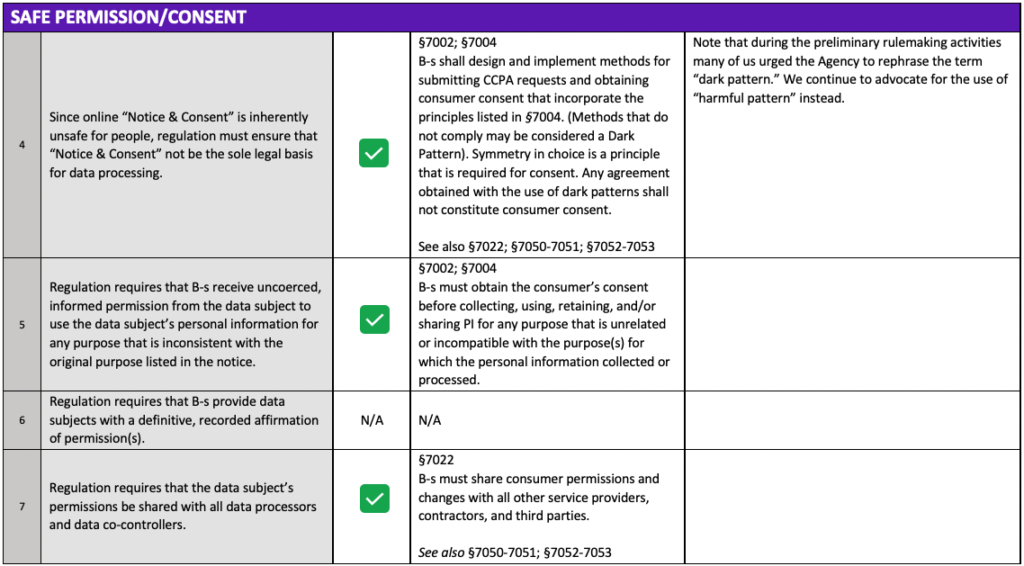
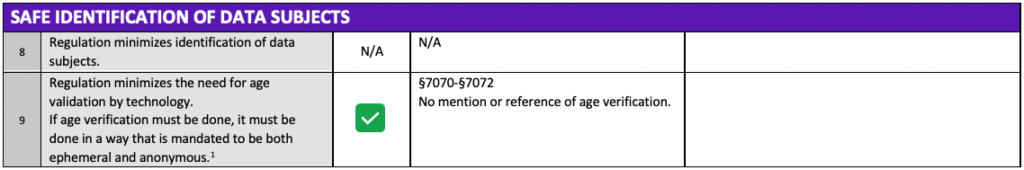
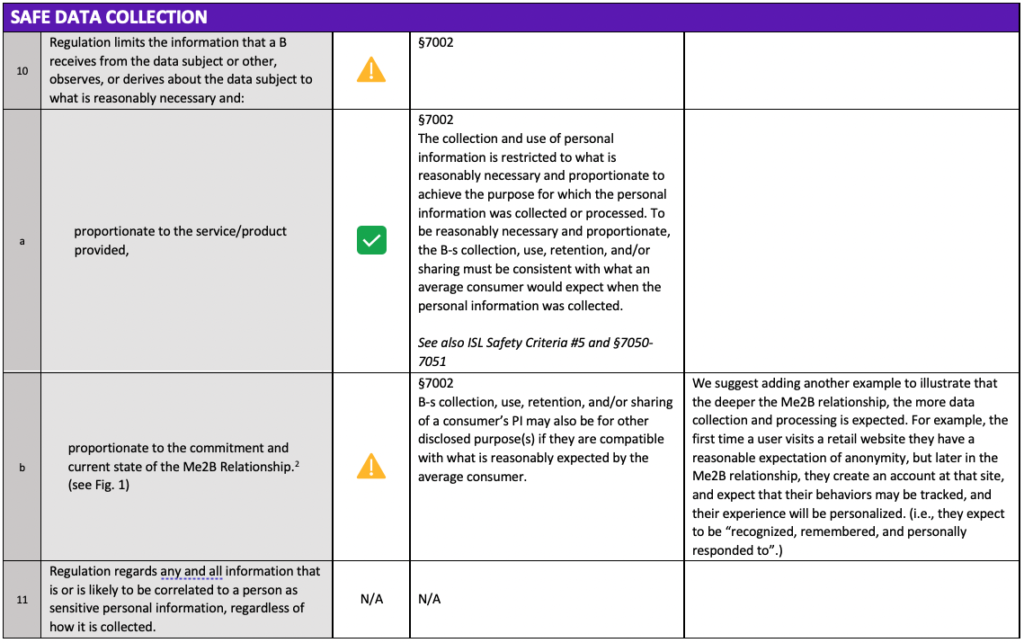
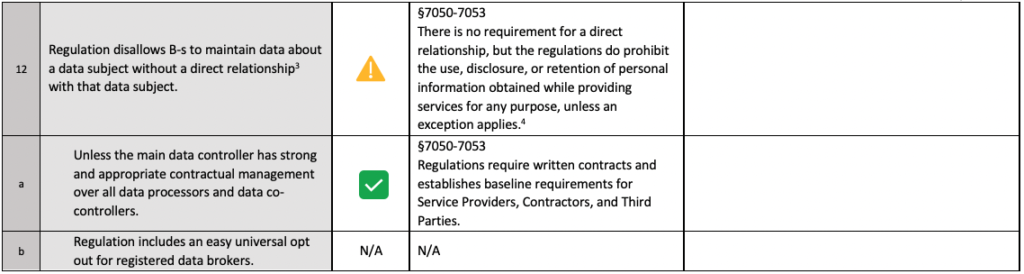
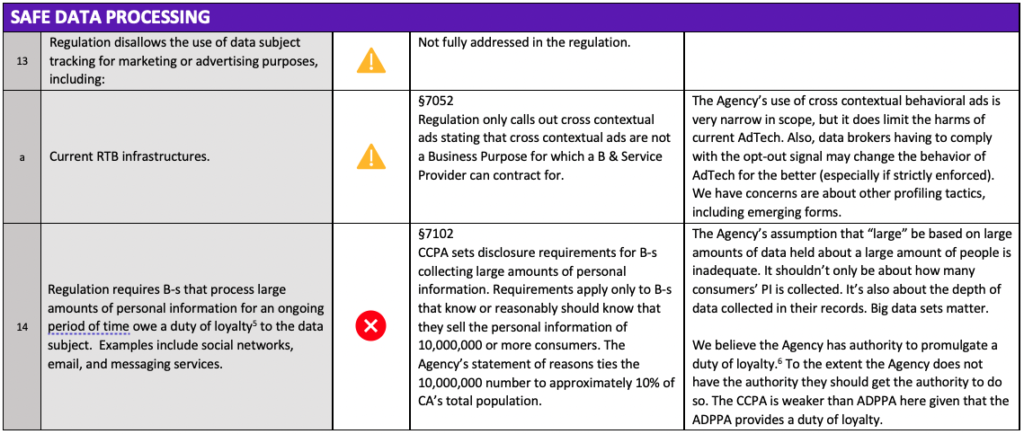
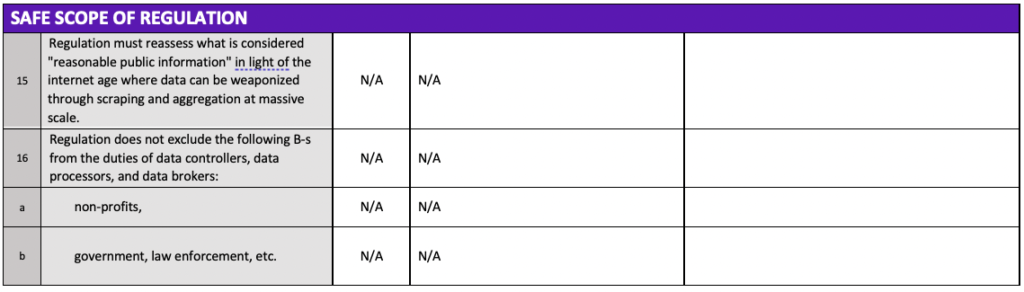
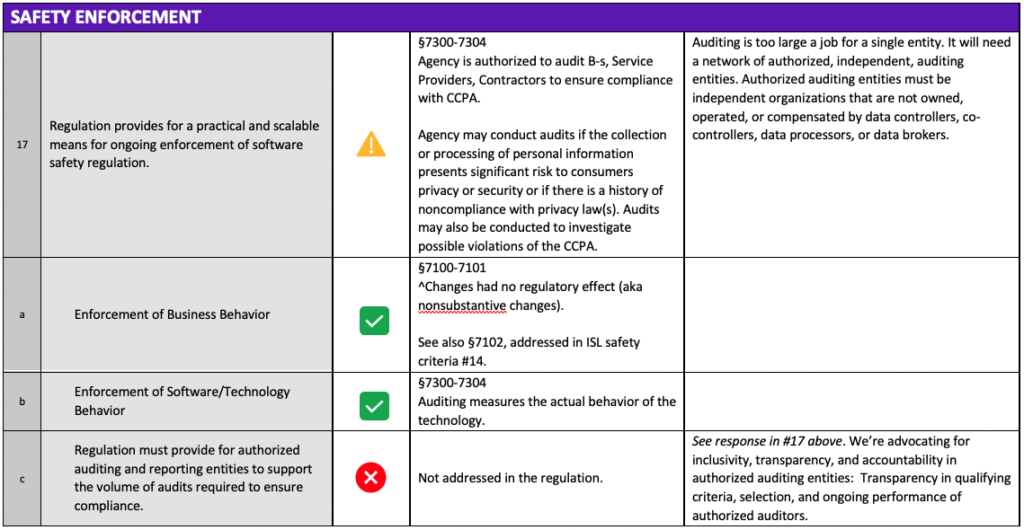
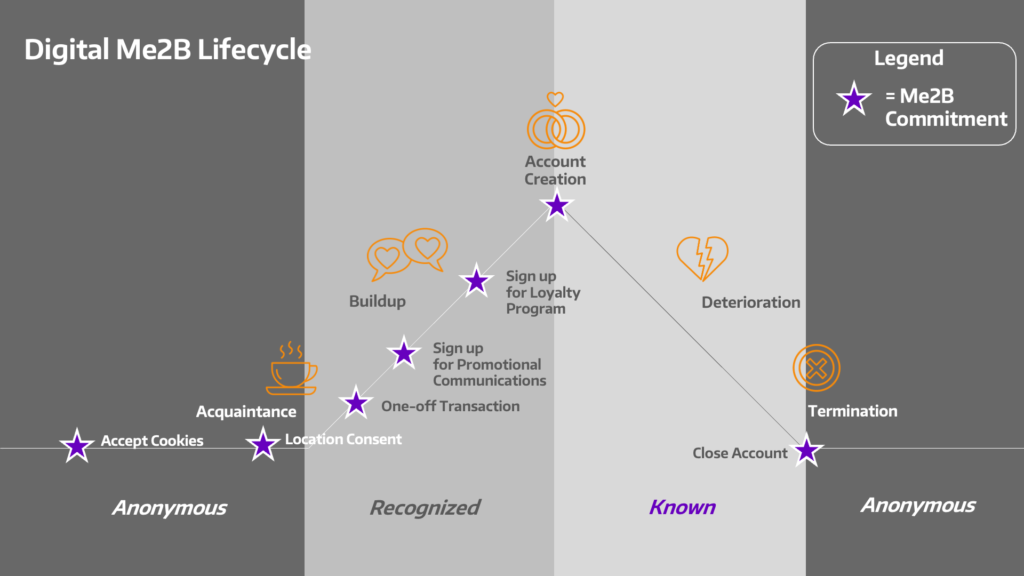
Figure 1: Me2B Relationship & Lifecycle (referenced in ISL Safety Criteria #10b)
Highlights from the CPPA’s Proposed Regulation
Below are five ways the CPPA has taken positive steps forward to advance safer regulations (please note that these highlights were not covered in full detail within our scorecard).
We applaud the CPPA for implementing regulations that:
Place restrictions on the overcollection of Personal Information
The collection and use of personal information is restricted to what is reasonably necessary and proportionate to achieve the purpose for which the Personal Information was collected or processed. To meet the reasonable and proportionate standard, the collection, use, retention, and/or sharing of personal information must be consistent with what an average consumer would expect at the time it is collected.
Thoughtfully address the topic of “Consent”
The regulation requires additional consent from consumers before their personal information is collected, used, retained, and/or shared for any purpose that is incompatible with the purpose for which the personal information was originally collected or processed for.
The regulation also incorporates the following guiding principles for Businesses to follow when designing and implementing methods to obtain consent:
- The language used must be easy for the user to read and understand
- There must be symmetry in choice
- See the various examples used to illustrate this concept under §7004(a)(2)
- Language or interactive elements that are confusing must be avoided.
- Double negatives should not be used.
- The toggles or buttons used must clearly indicate the user’s choice
- Manipulative Language or choice architecture should be avoided.
- This includes language that guilts or shames the user into making a particular choice or that bundles consent to subvert the user’s choice.
- Methods should be functional and easy to execute
- Methods should be tested to ensure that they do not add an unnecessary burden on the user.
Establish the Agency’s enforcement authority to audit the behavior of technology
We are thrilled to see that the Agency valued our public comments during the preliminary rulemaking to audit the actual behavior of the technology not just what the business says it’s doing (aka behavior of the Business).
Hold Service Providers, Contractors, and Third Parties accountable, even if the Business does not qualify under the law
Although there are instances where a business may not meet the criteria to be considered a covered “Business” under §1798.140(c) of the CCPA, other entities cannot hide behind that as an excuse!
Entities that process personal information on behalf of a non-covered Business, such as a non-profit, may be required to provide the same level of privacy as covered Business would under the law.
Sets clear contractual guidelines for Service Providers, Contractors, and Third Parties to follow.
Service Providers and Contractors
Regulations require written contracts that establish baseline requirements:
- Prohibiting the use, disclosure, or retention of personal information obtained while providing services for any purpose, unless an exception applies under §1798.145 of the CCPA.
- Granting the Business, the right to take reasonable steps to ensure that Service Providers and Contractors use personal information in a manner consistent with the Business’ obligations.
- Noting that reasonable steps may include audits or other technical testing at least every 12 months.
Third Parties
Regulations require written contracts that establish the following baseline requirements:
- The limited and specific business purpose or service must be identified in the contract.
- This disclosure is expressly prohibited from being made in generic terms.
- Personal Information can only be used for the limited and specified purposes identified in the contract.
- The Business has the right to take reasonable steps to ensure that the Third Party uses personal information in a manner consistent with the Business’ obligations.
- Giving Business the right to stop and remediate unauthorized use of Personal Information upon adequate notice.
- Third Party must notify the Business if it can no longer meet its obligations within 5 business days after making that determination.
- Third Party must honor the consumers opt-out signals.
Under the proposed regulations, violations may occur if personal information is collected, used, retained, sold, or shared but the Service Providers, Contractors, and/or Third Parties failed to have a contract or comply with the contract. Additional violations may occur if Third Party fails to check and honor consumers’ opt out preference signals.
Additional comments made to the Agency
[§7011(e)(1)]
- (b) “Categories of sources” is a good start but would be much better to list the companies.
- (e) “Categories of third parties” is inadequate; company names must be listed.
- (g) “Actual knowledge” should be changed to “constructive knowledge” which enables efficient enforcement while minimizing age verification. The current knowledge requirement isn’t adequately robust and leaves children and minors vulnerable.
- (i) “Categories of third parties” is inadequate; company names must be listed.
[§7051] “B(6)(a)(6) Collect or sell a consumer’s personal information if every aspect of that commercial conduct takes place wholly outside of California. For purposes of this title, commercial conduct takes place wholly outside of California if the business collected that information while the consumer was outside of California, no part of the sale of the consumer’s personal information occurred in California, and no personal information collected while the consumer was in California is sold. This paragraph shall not permit a business from storing, including on a device, personal information about a consumer when the consumer is in California and then collecting that personal information when the consumer and stored personal information is outside of California. “
- Why isn’t CPPA applying the same logic as GDPR Article 3 “Territorial Scope” item 1 such that Californians would be protected regardless of whether the processing takes place in California https://gdpr-info.eu/art-3-gdpr/?
- In general, Californians will reasonably expect to be protected everywhere. As written, these requirements could result in invasive location tracking of Californians.
- This section is important and needs to be carefully revised.